Why a Strong Password Matters
A password is the first line of defense for your data. Statistics show that over 80% of data breaches are linked to weak or compromised passwords. Attackers use brute force, dictionary attacks, and stolen password databases to gain access to accounts. A strong password makes these attacks virtually impossible.
What Makes a Password Strong
Password strength is determined by its entropy — a measure of unpredictability. The higher the entropy, the harder it is to crack the password. Entropy depends on two factors:
- Password length. Each additional character exponentially increases the number of possible combinations. A 12-character password is billions of times harder to brute-force than an 8-character one.
- Alphabet size. Using lowercase and uppercase letters, digits, and special characters expands the alphabet from 26 to 95 characters, greatly increasing the search space.
Entropy formula: E = L × log2(N), where L is the password length and N is the alphabet size. A 16-character password with the full alphabet (95 characters) has an entropy of about 105 bits — brute-forcing such a password would take billions of years even on powerful hardware.
Common Password Mistakes
Here is what you should definitely avoid:
- Using dictionary words. Passwords like
password,qwerty,dragonare cracked in seconds. - Adding predictable digits.
Password1oradmin123are not strong passwords, despite containing digits and uppercase letters. - Using personal information. Birth dates, pet names, phone numbers — all of this is easily found on social media.
- Reusing the same password. If one service gets hacked, attackers gain access to all your accounts (credential stuffing).
- Making minimal changes.
MyPass1,MyPass2,MyPass3— this kind of "rotation" adds no real security.
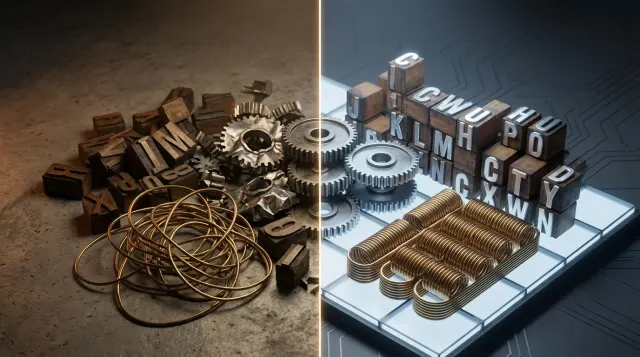
How to Generate a Strong Password
The best password is one that is randomly generated. The human brain is poor at generating random sequences: we tend toward patterns, favorite numbers, and predictable substitutions (@ instead of a, 0 instead of o). That is why you should use password generators.
Our password generator creates cryptographically strong random passwords of the desired length with a chosen character set. Recommended settings:
- Length: at least 16 characters for important accounts, 12 for less critical ones.
- Characters: lowercase and uppercase letters, digits, and special characters.
- Uniqueness: a separate password for each account.
The Passphrase Method
An alternative approach is using passphrases: several random words combined together. For example: correct-horse-battery-staple. Such passwords are easier to remember, yet with sufficient length (4-6 random words) they have high entropy. The key word here is "random": phrases from songs, quotes, and popular expressions will be cracked using dictionary attacks.
Two-Factor Authentication (2FA)
Even the most complex password can be compromised: phishing, keyloggers, database breaches. Two-factor authentication adds a second layer of protection:
- TOTP apps (Google Authenticator, Authy) — generate one-time codes every 30 seconds. A reliable and free method.
- Hardware keys (YubiKey) — a physical device, the most secure option.
- SMS codes — better than nothing, but vulnerable to interception through SIM swapping.
Enable 2FA wherever possible — especially for email, banking, cloud storage, and social media.
Password Managers
Remembering dozens of unique complex passwords is impossible. That is exactly what password managers are for: Bitwarden, 1Password, KeePass, and others. They store all your passwords in an encrypted vault, protected by a single master password. Benefits:
- A unique complex password for every site.
- Auto-fill forms without manual typing.
- Syncing across devices.
- Alerts for compromised passwords.
How Services Store Passwords
Reliable services never store passwords in plain text. Instead, they store a password hash — the result of an irreversible mathematical function. When you log in, the entered password is hashed and compared to the stored hash. Even in the event of a database breach, attackers only get hashes, not actual passwords. Learn more about hashing in our article on hash generation.
Frequently Asked Questions
What is the minimum password length?
The absolute minimum is 12 characters when using the full alphabet (letters, digits, special characters). For critical accounts, 16 or more characters are recommended. Each additional character significantly increases brute-force time.
How often should you change passwords?
Modern recommendations (NIST SP 800-63B) state: change your password only if you suspect it has been compromised. Frequent mandatory password changes lead users to choose weaker, more predictable passwords. One strong password is better than monthly rotation of weak ones.
How can I check if my password has been compromised?
Use the Have I Been Pwned service (haveibeenpwned.com) — it lets you check your email and password against a database of breaches. Many password managers also include this check. If your password is found in a breach — change it immediately.
Why do I need a password generator?
Humans are incapable of creating truly random passwords. We subconsciously use patterns, familiar words, and predictable substitutions. A password generator uses a cryptographically secure random number generator, ensuring maximum unpredictability.